Products
NDR - Network Detection and Response
Full Packet-Based Cyber Threat Hunting Solution
The full packet-based cyber threat hunting solution captures, stores, and analyzes all transmitted and received packets in the network to detect and respond to security threats.Unlike conventional security systems (such as IDS, SIEM, EDR), which rely on log-based detection, full packet-based solutions collect and analyze the original traffic in the network to identify threats comprehensively.
This technology is considered essential to counter advanced security threats such as Advanced Persistent Threats (APT), insider threats, ransomware, and zero-day attacks.
In the event of a security incident, packet data can be used to trace attack paths and conduct forensic analysis, providing strong capabilities for Incident Response (IR).
Our approach
Detection, Hunting, Forensic, Response
- Defined as NTA by Gartner in 2018
- Revised as NDR in 2020 to reflect market requirements for integrated response functions
Listed in Gartner’s NDR Market Guide for four consecutive years (2020–2023)
Asset Management
Identifies and classifies devices and provides risk scoring.
Hunting
Threat hunting is conducted based on TTPs (Tactics, Techniques, and Procedures).
XSec
Provides concrete evidence of attacks in incident response scenarios.
Response
Detected threats are reported through various channels.
Foundation

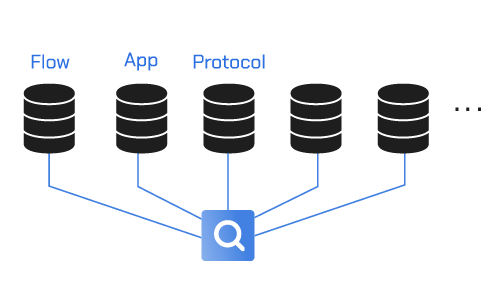
High-Performance Packet Stream Storage System
To ensure zero-loss storage in ultra-high-speed, large-scale network environments, a distributed storage system is required.
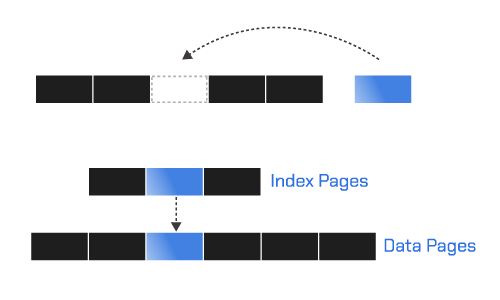
Pattern-Based Indexing System
After reassembling packets, performs pattern analysis and processes real-time indexing according to the corresponding application.
High-Speed Packet Search Method
Creates databases optimized for search conditions and enables fast searching of user-defined patterns.
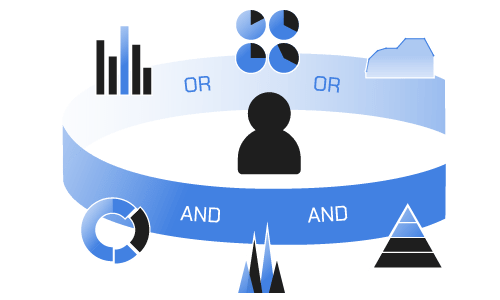
Scenario-Based Real-Time Attack Detection System
Utilizes a supervised learning-based threat hunting model to detect and identify sophisticated threats and anomalies in real time.